4 May 2026 / 7 minutes of reading
Cloud Security Audit vs. Cloud Penetration Test: Which Approach Should You Choose?
Imagine your team has just deployed a new cloud environment. The security manager asks: "Should we run an audit or a pentest?" The answer depends on one key question — what exactly do you need to know. And choosing the wrong approach can cost you months of false confidence.

A false sense of security is one of the most common problems in cloud environments and one of the main reasons we keep finding critical vulnerabilities in them.
Cloud security is most commonly addressed through two approaches: Cloud Security Audit and Cloud Penetration Testing. At first glance, they may look similar. But their goals, methodologies, and outputs are fundamentally different. This article will help you understand the difference and choose the right tool for your situation.
Cloud Security Audit: A Comprehensive Top-Down View
A Cloud Security Audit is a configuration- and compliance-oriented review of your environment. It uses a "white-box" approach, where the tester has full visibility into the cloud infrastructure. It is the most comprehensive view of security — combining automated tools, custom scripts, and manual analysis (AWS/Azure/GCP console, CLI). This is not about active attacks, but systematic identification of weak configurations. The audit is conducted in read-only mode.
An audit primarily answers the question: "Is the cloud correctly configured according to standards?" Its main goal is to identify gaps between the current state of the environment and security best practices (e.g., CIS Benchmarks, NIST, or internal policies).
Key areas of focus:
IAM Analysis
Identifying identities with low privileges that allow escalation to administrator level. Identifying roles/policies that violate the principle of least privilege.
Resource Misconfigurations
Detecting deployed resources with misconfigured settings that an attacker could exploit. E.g., an S3 bucket accessible from other accounts due to a flawed policy, missing encryption in transit, or missing logging.
Sensitive Data
Sensitive data accessible to anyone with account access. Hardcoded credentials in functions, data in environment variables, launch scripts, or logs.
Network Perimeter
Analysis of network infrastructure — e.g., unrestricted routing to the internet, missing restrictions in security groups, insufficient network segmentation.
Logging and Monitoring:
Verifying that critical services have logging enabled and are protected against tampering.
Advantages and disadvantages of a Cloud Security Audit
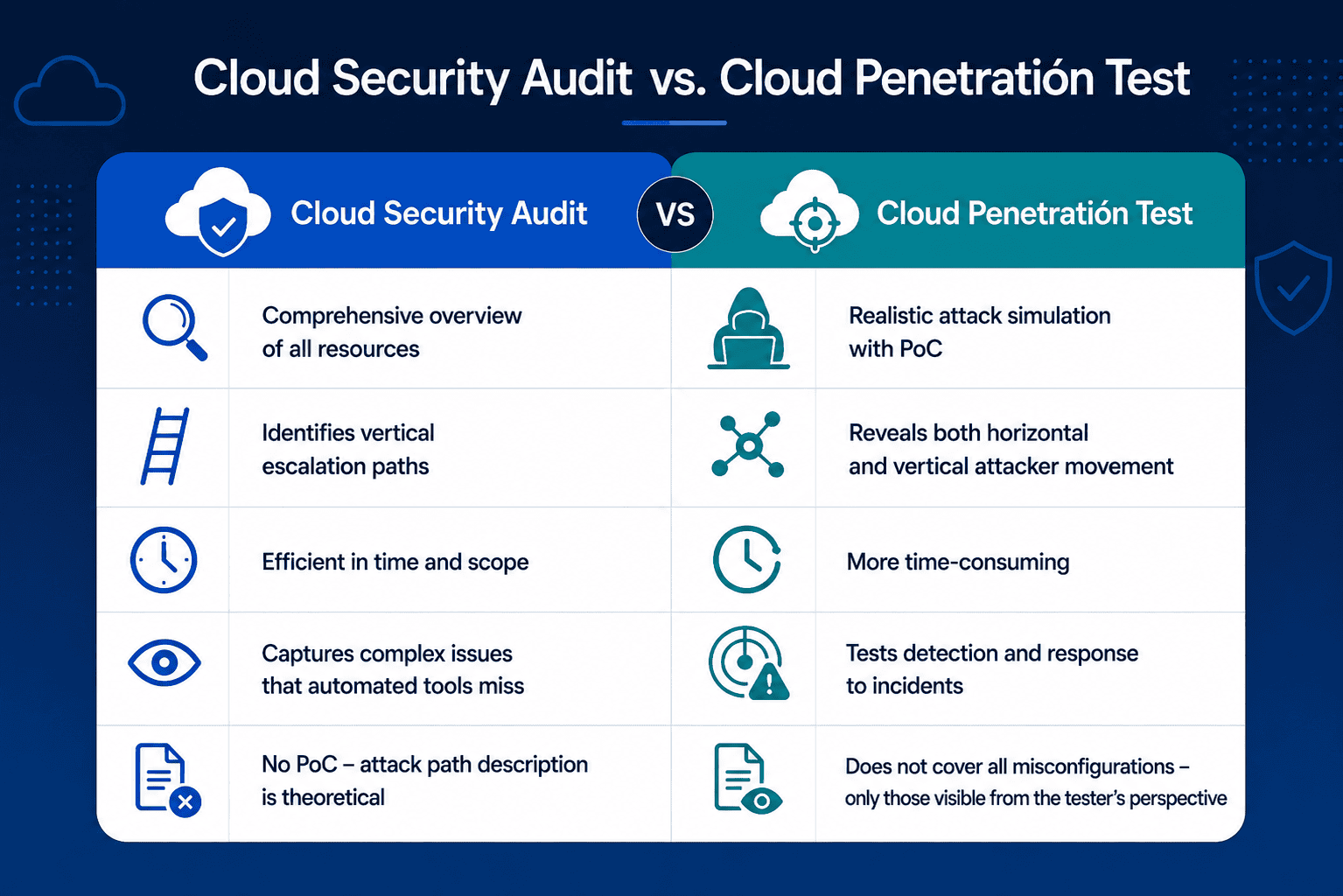
The main advantages of a Cloud Security Audit include: a comprehensive overview of cloud architecture, review of all resources, identification of vertical privilege escalation paths (from low permissions to admin), and detection of complex issues that CSPM (Cloud Security Posture Management) tools often miss. It is also time-efficient.
Its disadvantages include: less emphasis on detailed analysis of individual identities, typically no PoC (Proof of Concept) — only a theoretical description of the attack, and it usually does not cover lateral movement (unless specifically requested).
Cloud Penetration Test: Attack with a Specific Goal
Cloud pentesting is active security testing in the form of a simulated attack. Unlike an audit, it does not just evaluate configuration — it assesses the real impact of exploiting vulnerabilities. It is an "attack-driven" approach where the tester behaves like an attacker.
A pentest answers the question: "What can an attacker realistically obtain if they gain access to my cloud environment?"
It is a dynamic, scenario-based type of testing that simulates a real attacker progressively exploiting the environment. The test typically begins with a defined level of access (initial access), such as a low-privileged role (e.g., developer). Depending on scope, it can be white-box, grey-box, or black-box, with white-box or grey-box being most common in cloud environments. Black-box is less common, as without an initial foothold, it can be significantly limited in cloud architectures.
For cloud penetration tests, we recommend supplementary read-only access (as in an audit) to better understand the infrastructure and more efficiently identify possible attack paths.
Typical tested scenarios:
- Privilege escalation — moving from low permissions to administrator, exploiting IAM misconfigurations
- Data exfiltration — obtaining sensitive data (PII, databases) and transferring it outside the cloud environment
- Persistence — creating backdoor access, ability to survive in the environment without detection
- Bypassing controls — circumventing SCP/policy restrictions, bypassing WAF, evading automated remediation mechanisms (reactive controls)
Advantages and disadvantages of Cloud Pentesting
A pentest delivers concrete exploitation scenarios, proof of real impact (PoC), description of attack paths, and mitigation recommendations. Its main advantages are: realistic attack simulation, PoC for every finding, testing of detection and incident response, and revealing both horizontal and vertical movement. However, it is more time-intensive, does not uncover all misconfigurations, and provides a limited view based on initial access privileges.
Audit vs. Pentest: Overview of Advantages and Limitations
From Practice: What We Actually Found in the Cloud
Theory is one thing. To show why the choice of approach truly matters, we asked one of our senior pentesters three questions from real engagements.
The most common misconception: "Secure by default"
One mistake recurs across clients regardless of company size or cloud provider: the assumption that the cloud is secure out of the box. It is not. AWS, Azure, and GCP provide tools for secure configuration, but the actual setup is always your responsibility. Every bucket, every IAM role, every network rule is the responsibility of the team managing the environment. When clients grasp this, an uncomfortable surprise usually follows: they realize their environment only looks "secure" because no one from the outside has tested it yet.
The worst vulnerability in practice: SSRF that handed an attacker the keys
In terms of impact, one of the most serious findings is the combination of SSRF (Server-Side Request Forgery) and an overly privileged cloud role. The scenario goes like this: an application has an SSRF vulnerability, an attacker exploits it to access the cloud provider's internal metadata service, retrieves credentials for a cloud role, and if that role is administrative, they now have full control over the entire cloud account. The entire attack can take minutes. This is why auditing IAM permissions is not a formality.
The real impact of a misconfiguration: a bill for hundreds of thousands of euros
A cloud misconfiguration is not just a technical problem — it can be an existential one. An attacker with administrative access to an AWS account can deploy infrastructure within hours at a scale that results in a bill of hundreds of thousands of euros for the company. For most small and medium-sized businesses, this is not just an unpleasant situation — it can decide whether the company survives. This is not a hypothetical scenario. That is exactly why we recommend testing cloud environments before someone else does it with worse intentions.
Which Approach Should You Choose?
If you are dealing with basic hygiene and compliance, choose a Cloud Security Audit. It is the ideal solution when deploying a new cloud environment or wanting an overview of your security posture, or when scaling and growing your infrastructure. If you are testing production or sensitive environments and want to simulate a realistic attack, use a Cloud Pentest. It verifies the real impact of vulnerabilities on your infrastructure and tests your detection & response team.
Instead of General Recommendations — Concrete Situations and the Right Choice:
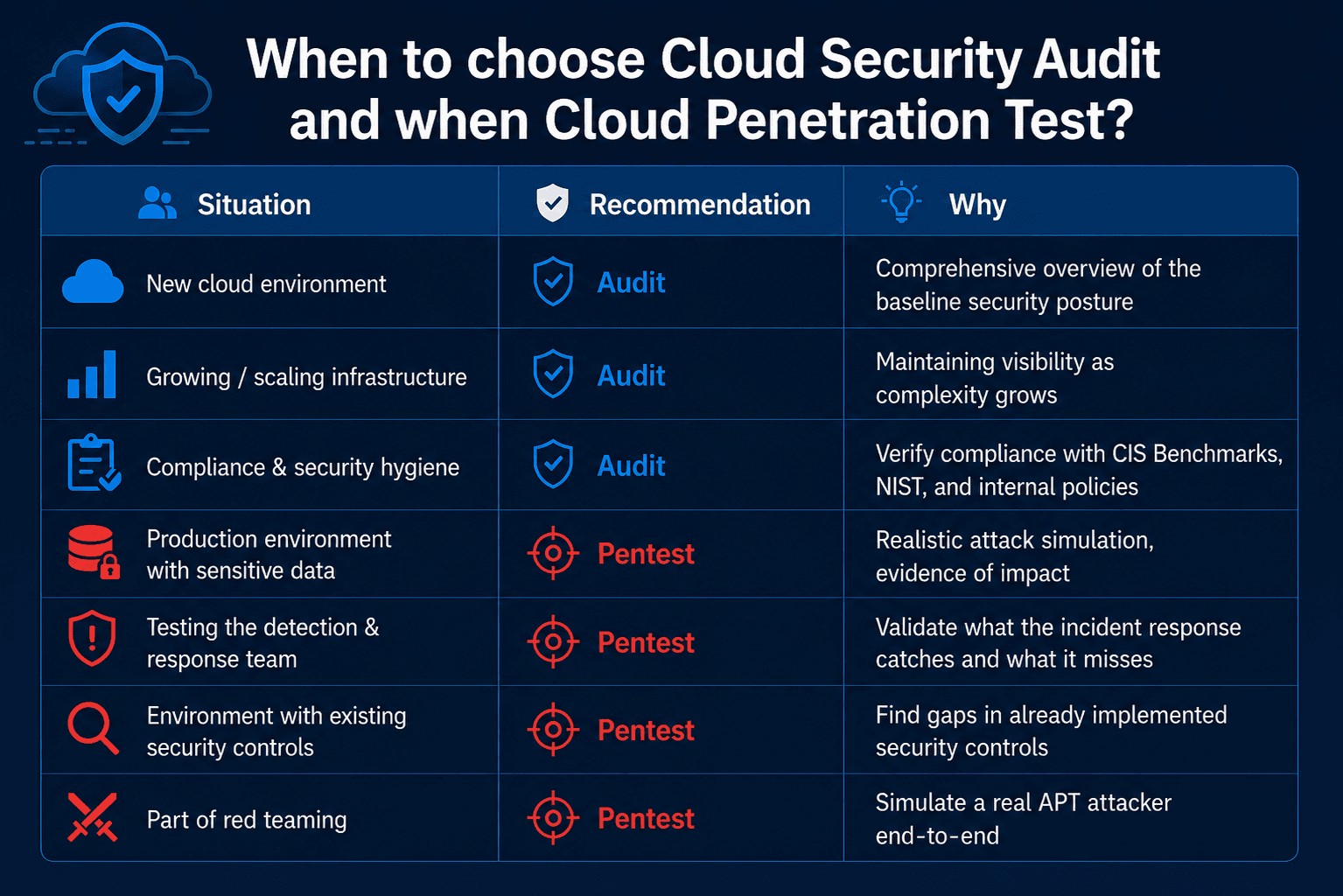
Quick rule: Audit if you are dealing with basic hygiene, compliance, or scaling. Pentest if you want to know what an attacker would realistically do with access they already have.
Not Sure What Your Cloud Needs?
Every environment is different. Some clients need an audit first to understand where they stand, and then a pentest to verify whether the deployed fixes actually work. Others have complex environments with sensitive data and need an offensive perspective from the start.
If you are not sure which approach is right for you, we are happy to help you define the scope — no commitment required.
Other interesting articles
All news