13 May 2026 / 7 minutes of reading
An €8 Smart Plug: Who Else Is It Sending Data About Your Home To?
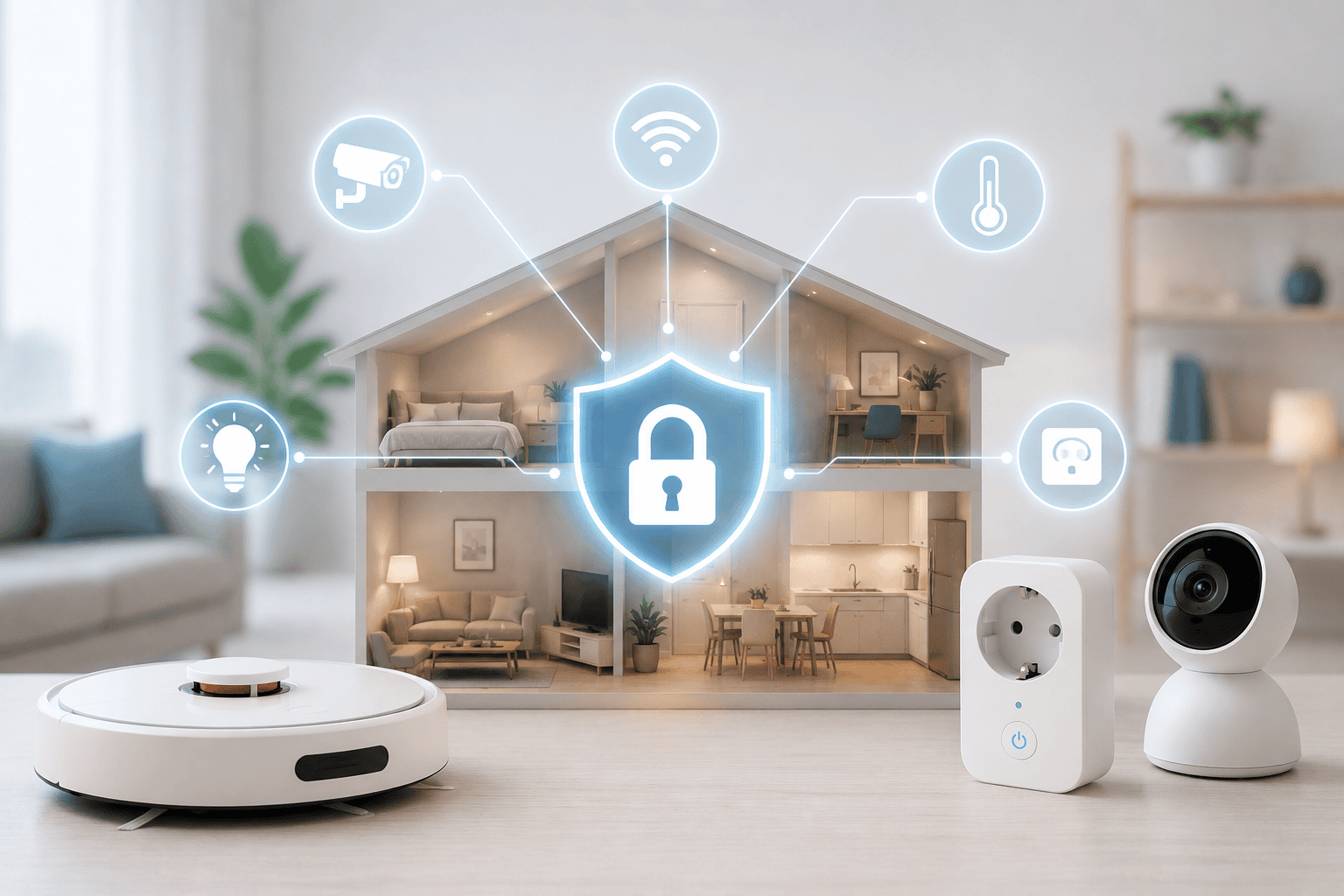
We buy them for the feeling of modernity and greater convenience. Smart plugs, thermostats and robot vacuums promise to save us time and money. But what if behind the “smart” label there is nothing more than simple logic that has completely forgotten what matters most: your security?

You pick up a smart plug on sale for a few euros. It has a nice app, measures power consumption and can turn off the coffee maker remotely. Great. But the moment price becomes the top priority, security drops far below the line. For manufacturers of cheap IoT devices, security is an extra cost that would “unnecessarily” raise the retail price for the consumer.
When “Smart” Doesn’t Mean Intelligent
We need to ask an important question. Are these devices truly intelligent, or do they simply execute basic logic? In most cases it is a straightforward set of rules such as: “If it is six o’clock in the evening, switch off the plug.” This functionality says nothing about how the device is protected against external interference.
At Citadelo we have been conducting penetration tests of IoT devices for years. Almost every device contains at least one vulnerability classified as high or critical. The most common issues we encounter are the same five problems:
- hard-coded credentials in the firmware,
- unencrypted communication between the device and the cloud,
- exposed debug interfaces (UART, JTAG) accessible to anyone with physical access to the device,
- insufficient or entirely absent authentication,
- an update mechanism with no signature verification.
Security analysts look at these devices in a completely different way from the average user. They want to know, for example:
- What permissions does the plug need to communicate? The principle of least privilege. A plug should talk only to its own control server or app. It has no reason to scan the local network or communicate with your printer, NAS or laptop.
- Can an attacker control it just by being connected to the same Wi-Fi? If so, that is a critical flaw. A properly designed device requires authentication regardless of who is on the network. The “I’m on the network = I have access” model has no defence in 2026.
- What happens if an attacker forcibly disconnects the device from the network? In an ideal world, nothing. The device attempts to reconnect; otherwise it stays offline. In reality, many switch to an open access-point mode with no password, exposing their configuration and sometimes even your Wi-Fi credentials to anyone nearby.
That last point is the decisive one. Many devices automatically switch to their own access-point mode when they lose connection – often without a password, to allow you to reconfigure them. An attacker can thus turn your light bulb into an entry point to your home network.
The Second-Hand Trap
A major risk that rarely gets talked about is buying this kind of tech second-hand. A used device may already be compromised. The previous owner, or someone who had access to it, could have injected malicious code into its firmware. A simple factory reset may not be enough. You could be buying a device that starts sending information about your network to an unknown third party from the very first moment. At Citadelo we therefore recommend investing in new, reputable devices rather than saving money here.
A Robot Vacuum as a Spy in a Secured Building
Let’s try a small thought experiment. Would you allow a modern robot vacuum with a camera into a strictly guarded military facility or a bank? If your answer is no, ask yourself why you let it roam freely around your bedroom or living room.
You might wonder what a vacuum cleaner needs a camera for. The technical answer is innocent enough: it is a sensor that evaluates position and maps the space to make cleaning more efficient. The critical risk, however, lies in where that data is processed. Does it happen locally on your vacuum? Or is a map of your flat and a video recording being sent to remote servers in a country you may never have heard of?
Smart cameras have the same problem. The convenience of checking from your phone whether everything is fine at home comes at the cost of the risk that a stranger is watching the same feed. Although these claims are sometimes difficult to prove, this is data that can reveal our private lives, our behaviour and our daily routines.
How to Stay Safe
According to the SonicWall 2024 Mid-Year Cyber Threat Report, the number of IoT malware attacks rose by 107 % in the first half of 2024. The average IoT device was under active attack for 52.8 hours. Attackers use compromised devices to build botnets that then carry out mass attacks against banks or large online services.
Five key steps:
- Cut them off from the internet. If your robot vacuum only needs a connection for the initial setup, block its outbound access in your router settings after configuration. It will do its job just fine without the internet.
- Create an isolated network. If you want to control your devices from your phone while on the go, set up a separate network for them.
- Change default passwords immediately after installation. Botnets like Mirai still work today precisely because millions of devices around the world run on their default credentials.
- Keep the firmware updated. If the manufacturer does not provide regular updates, that is a red flag. The device will not be patched when a new vulnerability is found – and that can be a matter of months.
- Buy from reputable manufacturers. A price of a few euros sounds tempting. But if the manufacturer has no clear data-processing statement and offers support for less than a year, you are saving in the wrong place.
These steps ensure that even if an attacker breaks into your smart plug, all they see in the system is another light bulb. They will not reach your computer with your photos, your work, or your bank account access. Smart technology makes an excellent servant but can be a dangerous master. Before you add another device to your home, ask yourself whether the convenience is worth the risk.
A smart home is not a bad technology. It simply requires a grown-up user. One who knows that every connected device is, first and foremost, a computer. And every computer can be exploited.
If you manufacture, distribute or deploy IoT devices in a corporate environment, IoT penetration testing is something that should be on your list before a product goes to market – not after the first incident. At Citadelo we have years of experience in this area, from firmware analysis and reverse engineering through hardware interface testing to cloud infrastructure audits.
Other interesting articles
All news